MALWARE PATROL FOR MIKROTIK
MIKROTIK INTEGRATION OPTIONS
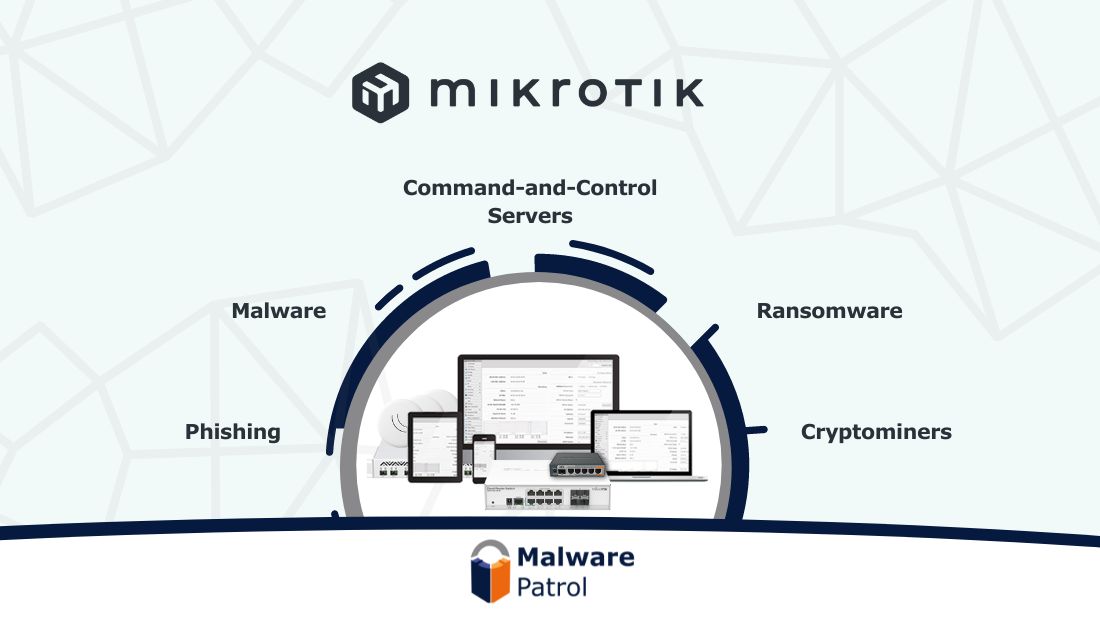
Malware Patrol offers three feeds formatted for MikroTik devices. Combined, these feeds provide protection against a wide range of threats from active, malicious campaigns:
1. Malicious Domains – Prevents access to sites hosting malware, ransomware, phishing, cryptominers, and command-and-control servers (C2s) for over a hundred malware and ransomware families. Blocking C2 traffic alone breaks the cyber kill chain by preventing additional payload downloads, data exfiltration, and ransomware file encryption.
2. DNS-over-HTTPS (DoH) Servers – This feed gives security teams control over the use of DoH in their environment. DoH wraps DNS queries in an HTTPS request, which can disguise malicious traffic. Several malware families take advantage of this to use DoH for their C2 communications.
3. Tor Exit Nodes – Malicious actors use Tor to mask their identity and to relay C2 communications. It is generally advisable to block traffic to and from Tor exit nodes. (See what CISA has to say about this topic.)
Mikrotik Router Configuration Guide
Click here to access our detailed MikroTik configuration guide. It provides step-by-step instructions for configuring your MikroTik router to filter malicious domains. This will protect your network and users from accessing phishing and cryptomining sites as well as malware and ransomware infections.
Check out the video below to learn more about Malware Patrol and how we help businesses to improve their security.
About Mikrotik
“MikroTik develops and sells wired and wireless network routers, network switches, access points, as well as operating systems and auxiliary software. Their RouterOS has a very powerful firewall implementation with features including:
- stateful packet inspection
- peer-to-peer protocols filtering
- traffic classification by:
- source MAC address
- IP addresses (network or list) and address types (broadcast, local, multicast, unicast)
- port or port range
- IP protocols
- protocol options (ICMP type and code fields, TCP flags, IP options, and MSS)
- interface the packet arrived from or left through
- internal flow and connection marks
- DSCP byte
- packet content
- rate at which packets arrive and sequence numbers
- packet size
- packet arrival time”
